Checker ATM Security®
Comprehensive and Effective Solution Designed for ATMs
General Information
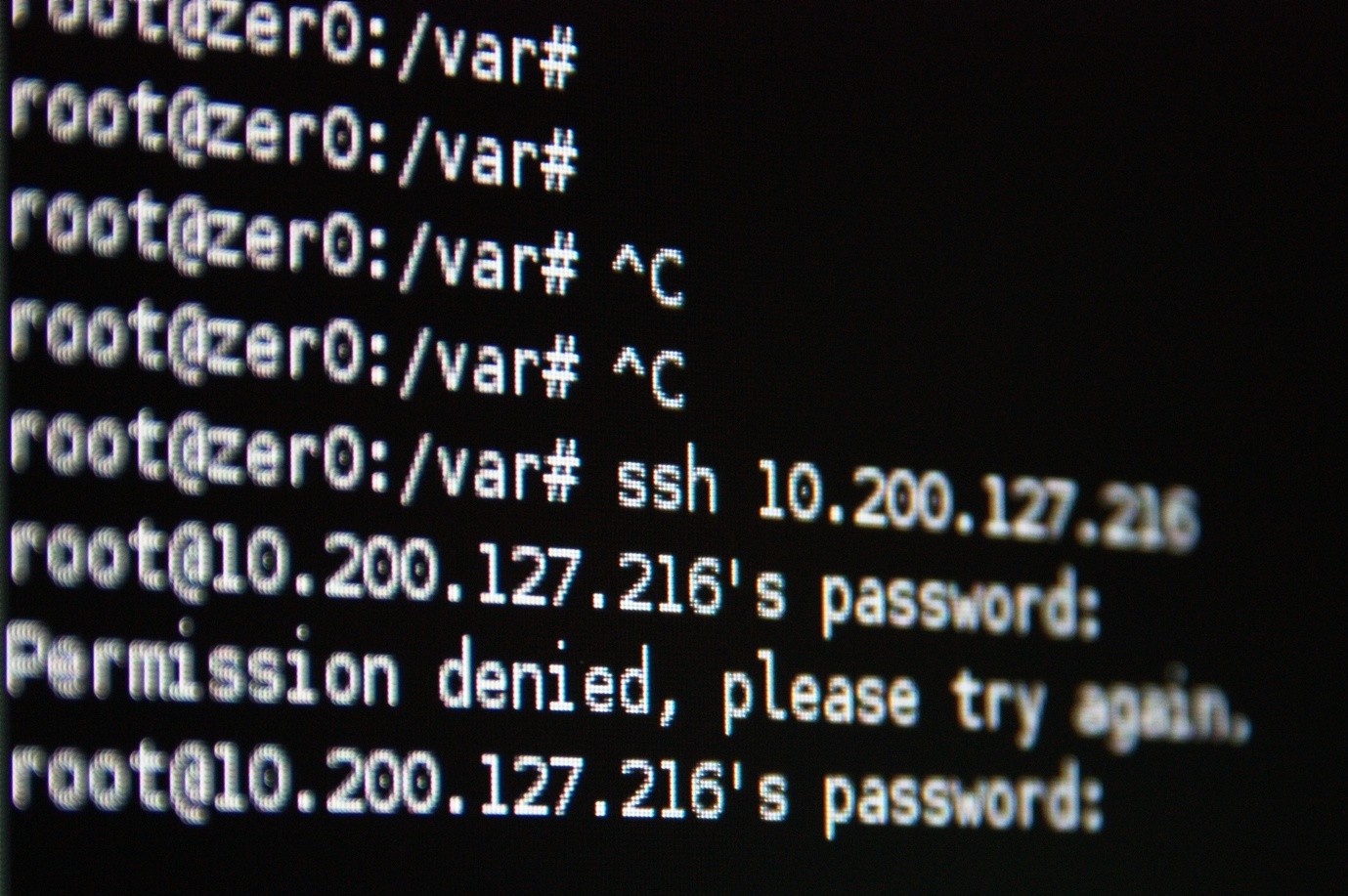
Cybersecurity product specifically designed for financial self-service networks.
Checker ATM Security® is a world-class cybersecurity product specifically designed for ATMs and kiosks. Checker® will help you protect your ATMs from logical fraud while meeting applicable PCI-DSS requirements quickly and effectively, even for unsupported versions of the ATM operating system.
- Checker® provides a set of tools for creating, implementing, and maintaining server-side security policies and applying them on the agent side (ATM).
- ATM security policies are a consistent set of standards, principles, and practices that determine how to implement and manage security on the ATM network.
- These security policies can be configured flexibly, which makes it possible to set a common policy or a close definition.
- Security policies can be defined based on roles or users, which integrates the policy definition with the repository of existing users.
- Integrity protection: Checker® validates the integrity of the critical processes and resources of the operating system using digital signatures and SHA-256 hashes.
- Resource usage protection: the use of operating system resources (log, libraries, and controllers) is granted or denied for each process.
- Multi-version compatibility: validation of Checker® integrity is compatible with different versions of the same (authorized) program or resource.
- Whitelistling: Checker® maintains a list of permitted and approved processes. Processes not included on this list will be blocked.
- Integrity protection: the integrity of the processes included on the whitelist and the corresponding resources are validated. Processes or resources illegally altered will be blocked and reported.
- Resource use protection: Checker® controls the utilization of local resources filtered by whitelisted processes.
- Java resource loading control: Checker® maintains a detailed list of all resources loaded by the Java Virtual Machine in ATMs. Loading of non-permitted Java resources will be blocked.
- Scripts and interpreted code: Checker® controls the execution of scripts and other types of interpreted code that runs in the interpreter processes macro.
- Plug & play hardware protection via syslog protocol, Windows event log, local auditing log in file: Checker® detects the connection of new hardware and allows or denies the assembly.
- Device access control: Checker® filters access to connected devices on a process-by-process basis.
- USB drive control: Checker® provides reliable control of authorized USB units and conducts secure maintenance.
- Mass storage USB device control: Checker® allows a whitelist and a blacklist to be defined for this kind of USB.
- File system protection: validates access to local files and directories on a process-by-process basis.
- Integrity protection: checks the integrity of sensitive data files and detects unauthorized modifications.
- Data loss prevention (DLP) for ATMs: detects track2 card data stored locally in ATMs. Any writing that follows a track2 pattern is reported.
- Restrictions based on roles or users: user control is based on a list of authorized users and groups, both local and those defined by Active Directory.
- Keyboard control: all ATM keyboards, except the PINPADs, can be partially or totally disabled so that they cannot be used or their use is partially limited. Limitations are selected from a predetermined list of options based on specific keys or groups of keys.
- External pluggable storage device control: Checker® detects the connection of such devices and allows or denies assembly, reporting this situation as a security event.
- ATM hard disk encryption can be fully managed from the Checker® console, including remote commands to encrypt or decrypt ATM disks. Key management is automatic and transparent to the user.
- Zero downtime: the encryption can be commanded from the server and the disk can undergo the encryption process while the ATM keeps operating.
- Smart Environment Detection: decryption is only possible for a specified ATM environment defined as a configurable combination of identifiers associated with the ATM hard disk, the ATM hardware, and the ATM network.
- Network Manager: through communication with agents, the Checker® console operator can apply new security policies, manage security execution mode, upgrade Checker® software, request remote system shutdown, and more.
- Security Policy Management: the Checker® console includes a very complete and intuitive security policy editor. Learning mode allows easy and fast security policy creation from existing and trusted ATMs.
- Real-time security monitoring: the Checker® server receives security events generated by agents in real time. These events are shown in a security dashboard, enabling easy security monitoring of the whole ATM network.
- Management delegation: management functions are assigned based on an RBAC matrix, depending on the context and the hierarchically-defined ATM network.
All relevant events that occur in the ATM and are controlled by Checker® are registered locally in the ATM and centralized on the server. These events include the following:
- Attempts to breach the policy being applied at any given time.
- Failed signature validations.
- Requests to execute commands received from the server.
- Results of executing commands.
- Agent execution errors.
- Other events of interest from a security standpoint (e.g.,shift to critical mode, detection of an attempt to end an Agent process or change the ATM’s IP).
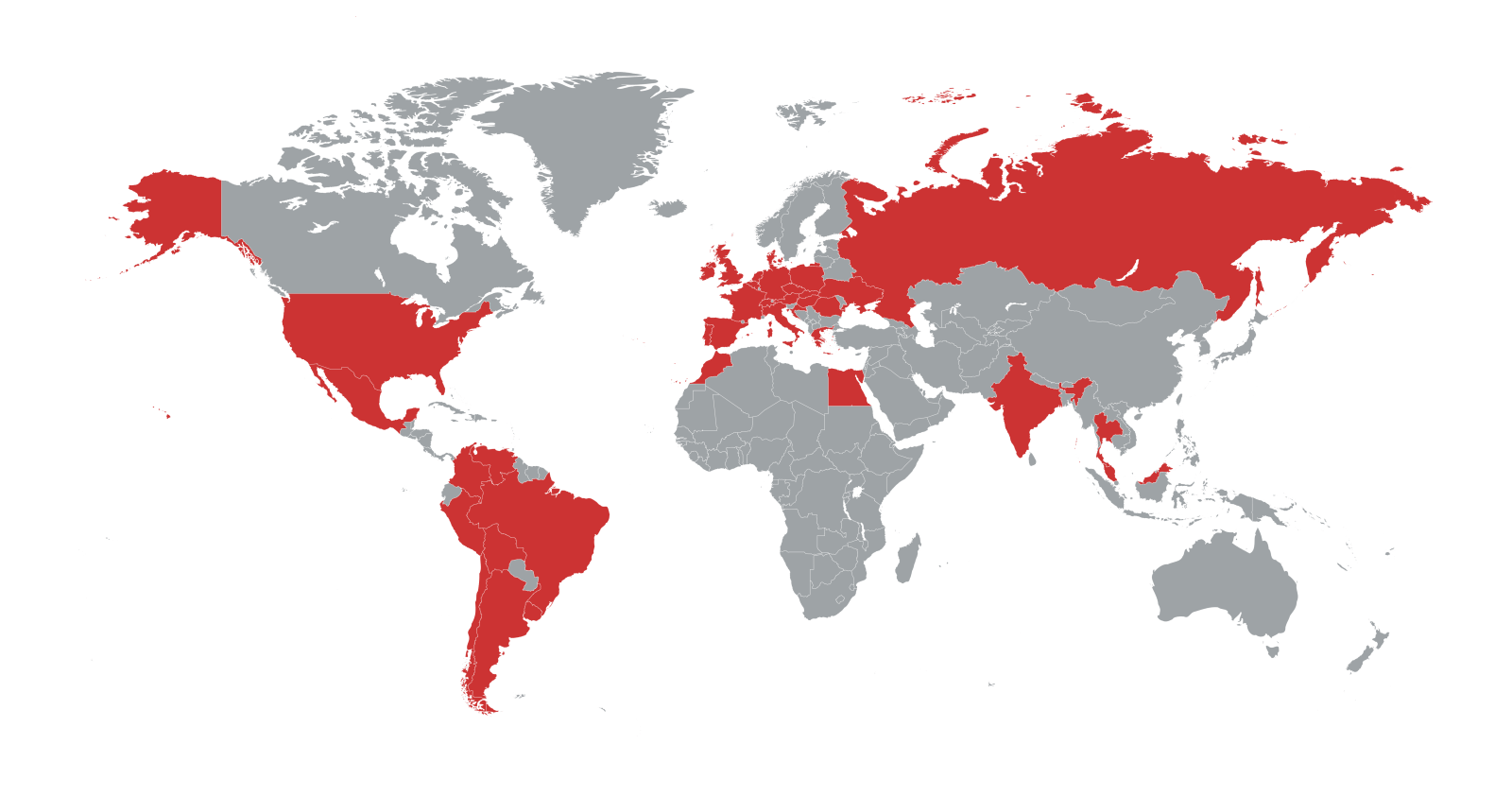
Checker® supports a wide variety of operating systems and platforms, so it is suitable for almost any ATM in the world:
- Compatible with Windows NT4, Windows XP, Windows 7, Windows 8, and Windows 10.
- Compatible with the 32- and 64-bit versions of Windows 7, Windows 8, and Windows 10.
- Compatible with BIOS and UEFI firmware.
- Compatible with discs formatted in GPT and MBR.
Checker ATM Security resources
Other resources
FF News: Video interview Pedro Celis, Product Manager on Checker ATM Security® at GMV
https://youtu.be/acApZmjvC5c